With the increased need to enable people to “Work From Home”, setting up VPN access is a vital step to ensure a secure connection to the work environment.
Ubiquiti EdgeRouters have the capability to support all current standards of VPN access including PPTP, IPsec Site-to-Site and L2TP IPsec. L2TP IPsec is the preferred method of connecting an individual to a work environment. EdgeRouters only have a GUI to enable the first two options. In order to configure L2TP, a series of Command Line instructions are required. We’ll come back to that in Step 2.
Step 1. Setup and configure the Radius Server
Log in to your Synology NAS and launch Package Center.
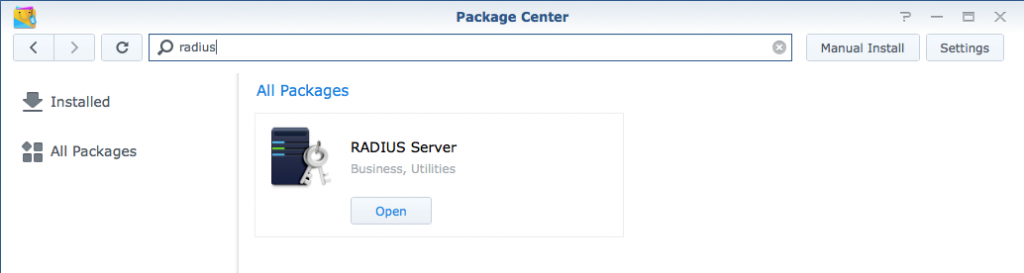
Under All Packages, search for Radius. Install the package “RADIUS Server” and then Open it.
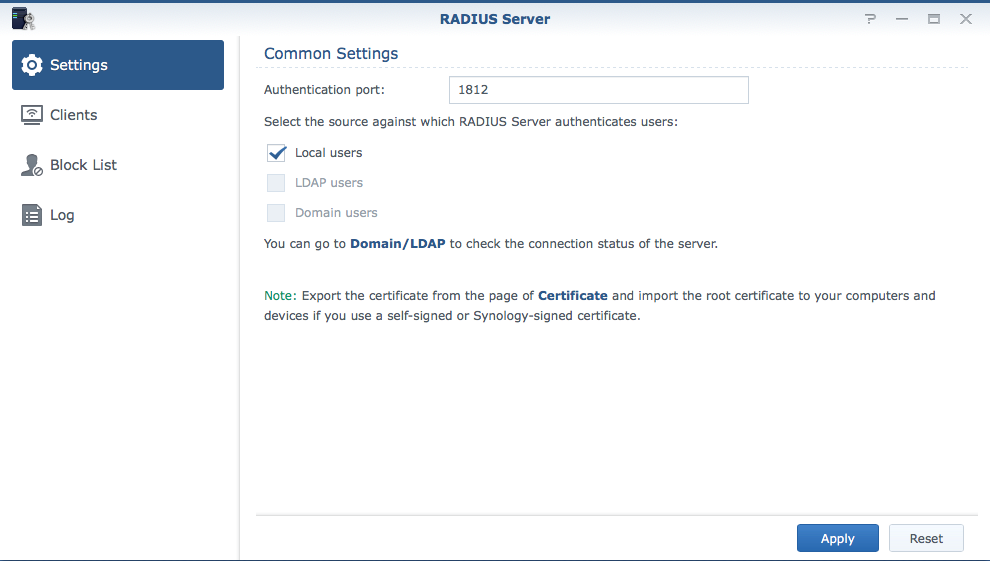
Under Settings, choosing the default port of 1812 is fine. Choose where the users you are wishing to link reside. In the case below, they are local users.
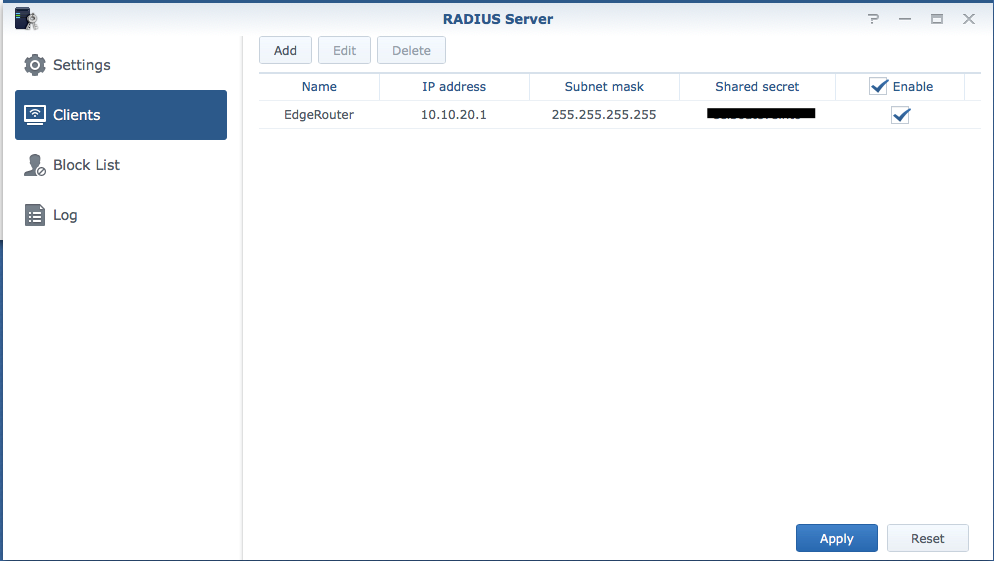
Next, select Clients and fill in the appropriate details. In the example below, the EdgeRouter’s IP Address is 10.10.20.1. Choose a complicated “Shared Secret” and make a careful note of it as you will require this in Step 2.
Step 2. Setup and configure the EdgeRouter
Important Tip before running commands in a CLI.
Note: In the top right hand corner of the EdgeRouter web interface is a “CLI” button (as per below).
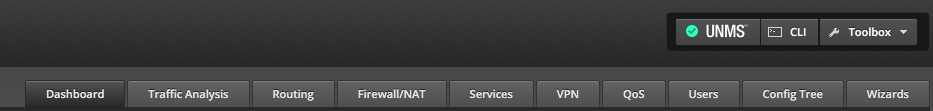
This will launch a pop-up CLI interface window, however it is not very usable as you will not be able to copy and paste commands into it.
Instead launch an SSH session in Terminal. In the example below I wish to connect to my router at 10.10.20.1, so the command would be:
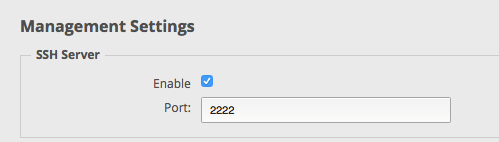
If you have changed the default SSH port from 22, you’ll need to add the -p parameter.
ssh [email protected] -p 2222
This article details the instructions required to enable your Ubiquiti EdgeRouter to act as an L2TP IPsec VPN Server. If you were only enabling access for one or two users, then you would not need to setup a Radius Server, however when there is the need for a large number of users to have VPN access, using a Radius Server will pass through each user’s credentials from the Synology NAS, whether they are Local users, LDAP users or Domain users.
https://help.ubnt.com/hc/en-us/articles/204950294-EdgeRouter-L2TP-IPsec-VPN-Server
Note: In section 3 of the article above, when configuring for a Radius Server, choose the “Optional” instructions.i.e. Replace the following two lines
set vpn l2tp remote-access authentication mode local
set vpn l2tp remote-access authentication local-users username password
with
set vpn l2tp remote-access authentication mode radius
set vpn l2tp remote-access authentication radius-server
key
Note that the authentication mode will be “radius” rather than “local” Also, the step above is where you enter the IP Address of the Radius Server and the Shared Secret you chose in Step 1. (If necessary this can be changed later in the Config Tree - see below)
You will need to decide on an address pool for Step 4 of the article. Typically it will be a range that could accomodate the maximum number of users you would want connected simultaneously.
In Step 5 of the article, you will choose the internal DNS server address. This will ensure that internal resources properly resolve.
Select the appropriate WAN interface of your router in Step 6 and also in Step 7.
Commit and Save your configuration and you’re done!!
One final step you may have to do is to set the Authentication Port number that you selected for the Radius Server. This can be done in the GUI using the Config Tree.
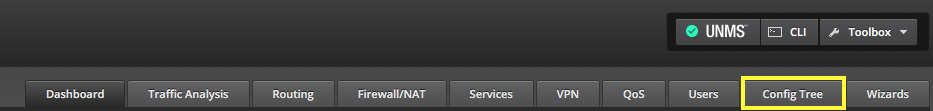
On the left hand side of the EdgeRouter interface when you select Config Tree you will see all of the configuration. Each section can be expanded. Note, passwords are displayed in clear text.
Expand vpn / l2tp / remote-access / authentication / radius-server / ip address of radius-server
In the example below, the Synology NAS address is 10.10.20.13. Here we see the Shared Secret and the Port Number. Make sure you select the correct port number. If you changed the value, press the Preview button at the bottom to save the configuration changes.


